An often recurring problem online is how to prove you’re eligible to access a particular resource, if that resource is limited to people belonging to a certain group. This problem occurs, more abstractly, if the resource is managed by some organization that is not itself responsible for determining who is eligible. Examples: sites accessible to physicians, but not run by the organization that actually licenses physicians. Or, sites accessible to holders of particular certifications, but not run by the certification authority. One of those problem children is the CISSP cert, since there are a number of resources for holders of the CISSP cert.
The CISSP forum is a place where only CISSPs can read and write. ISC2, the organization that issues the CISSP certificate, takes care of registering users on that forum, so that way, the selection of participants is ensured. But there are other resources that are exclusively available to CISSPs, like being in the CISSP LinkedIn group or accessing CISSP specific Wiki sites or archives. These “third party” resources have no easy way to determine who is actually a CISSP and who is not, particularly since ISC2 is certainly not giving just anyone access to their database. Worse, many CISSPs want to register to those third party resources using an email address that is not necessarily known to ISC2, since many of us have multiple email addresses.
The reason I present a solution to this little problem in the form of a protocol is that it is probably of a more general interest. Just try the protocol and you’ll probably see a lot more uses for it.
I set up a fake authority site, which represents ISC2 in the above scenario and another fake site that promises to hand out weekly free beer over email to any bona fide CISSPs who register. (I still have to figure out the actual beer delivery logistics, so I’m not honouring my commitments in this respect.)
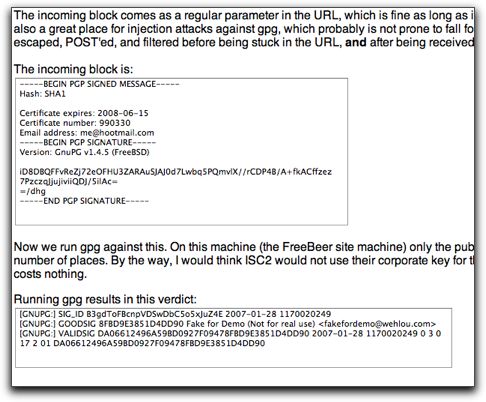
To test it out, first go to the “Free Beer” site and follow the instructions. The Free Beer site will redirect you to the “ISC2 site”, where you can get a digitally signed certificate that certifies that you’re a bona fide CISSP, so to speak.
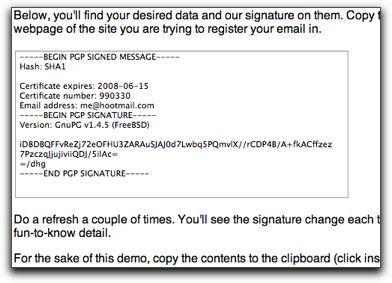
Copy and paste that certificate back into the Free Beer site, have it verified and parsed, and you’re supplied with free beer every week until your CISSP cert expires. Or would be, if any of the above was true, which it isn’t.
You can just as well use the authority site to produce a signed statement that you can paste into an email. The advantage of that is that the receiver’s email program will automatically verify the signature as soon as the email is viewed, if it has the corresponding public key.
Now, go play with it. It’s fun.
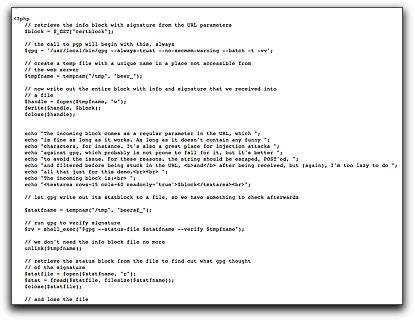
I even provide you with the full source for all the pages, which is surprisingly little and simple code. You’ll find links to the source in the pages themselves.
The current implementation assumes you’ve got gpg (or pgp) and php installed on your webhost, but practically every decent webhost has, as far as I know. That’s the only requirement, actually.
Please note: I’m just using ISC2 and the CISSP certificate as an example here. That’s because I think they should use this protocol, but there are lots of others that could use it just as well.

Thanks, for the great idea…
Bill