This past week, Apple announced their first ARM M1 based computers, also called “Apple silicon”. As expected, they’re pretty good. Not so expected is just how much better they are than the previous Intel-based machines. It’s an understatement to say that the Intel machines were blown away (somewhat to my chagrin).
Continue reading “Apple M1 and the future”Category: Hardware
Storage and backups
When you do video production of any kind, you quickly run into two problems, namely having the files organized so that you can effectively find them, and secondly, the insane volumes of data to manage. I sortof knew that movie studios had massive data volumes, but I didn’t realize that even a moderate operation like ours would produce so much data.
Continue reading “Storage and backups”iPad stopgap
What I really want and need is a real laptop like the MacBook Pro 16”. But as I already posted about that didn’t turn out as well as I hoped. So now I have to wait until the next generation of the flagship MacBook Pro before trying to order again.
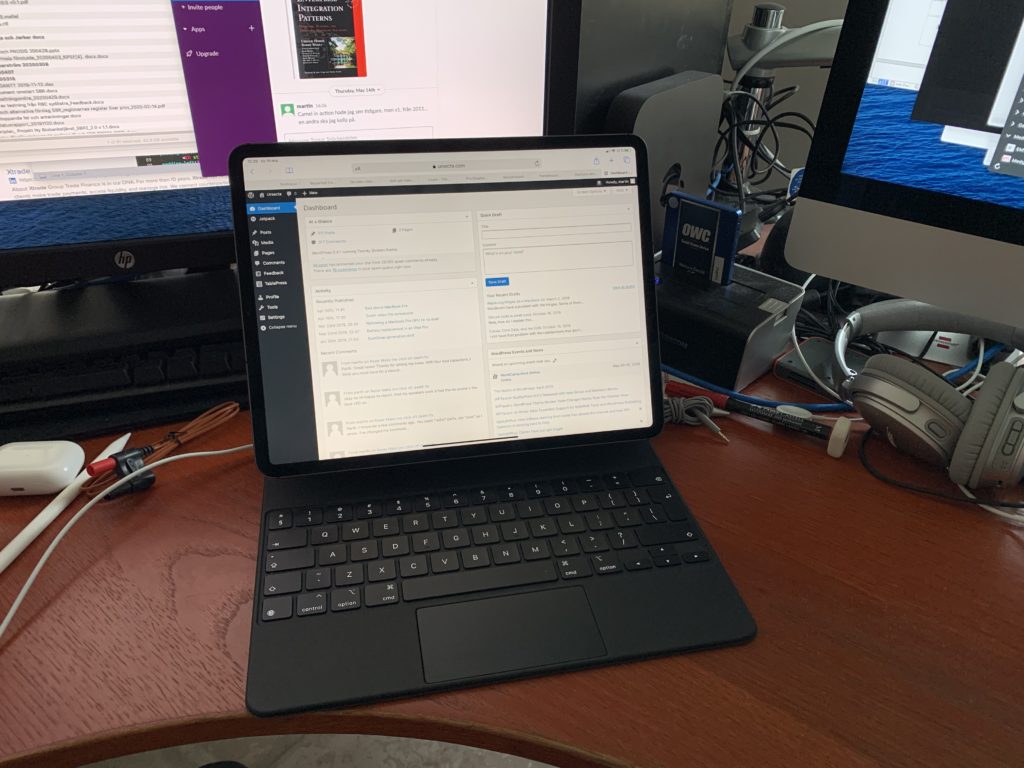
Meanwhile, my wife got the other MBP 16” and my iPad Pro for making online math lectures, so I was left with nothing, or seen as a positive; an opportunity to buy a new iPad Pro with the Magic Keyboard case. The iPad Pro arrived yesterday and the keyboard just an hour ago.
First impressions (I’m writing this on the new keyboard, by the way) are: it’s an amazingly nice keyboard to type on. It’s sturdy and very stiff. You can lift the whole thing by a corner without any bending. It’s also the exactly right angle for the screen.
I’m writing both in Swedish and in English, and occasionally in Dutch, on my keyboards, so I always order “International English” and then switch keyboards in software. That works just fine on this keyboard, too. I’m still getting used to there not being any escape key or home key (the latter is replaced by a trackpad gesture). The cmd-. combo sometimes works as an escape, but mostly not. Applications clearly weren’t written with keyboards in mind for the iPad.
I’ll probably be back with more impressions later on, but for the moment I’d just like to keep on writing, even if it makes no sense. That’s the kind of satisfying feel this keyboard has.
Sad about MacBook Pro
Having lost my 17″ Macbook Pro from 2011 to the ravages of time, in december I bought a Macbook Pro 16″, the larger standard config, the one with 2.3 GHz CPU, Radeon 5500M 4 GB, 16 GB RAM, and 1 TB SSD. It’s a fantastic machine, and I was very happy with it. So, naturally, I gave it to my wife and ordered another one for myself, but this time a litte more pimped out; 2.4 GHz CPU, Radeon 5500M 8 GB, 32 GB RAM, and 2 TB SSD. I think that was a mistake.
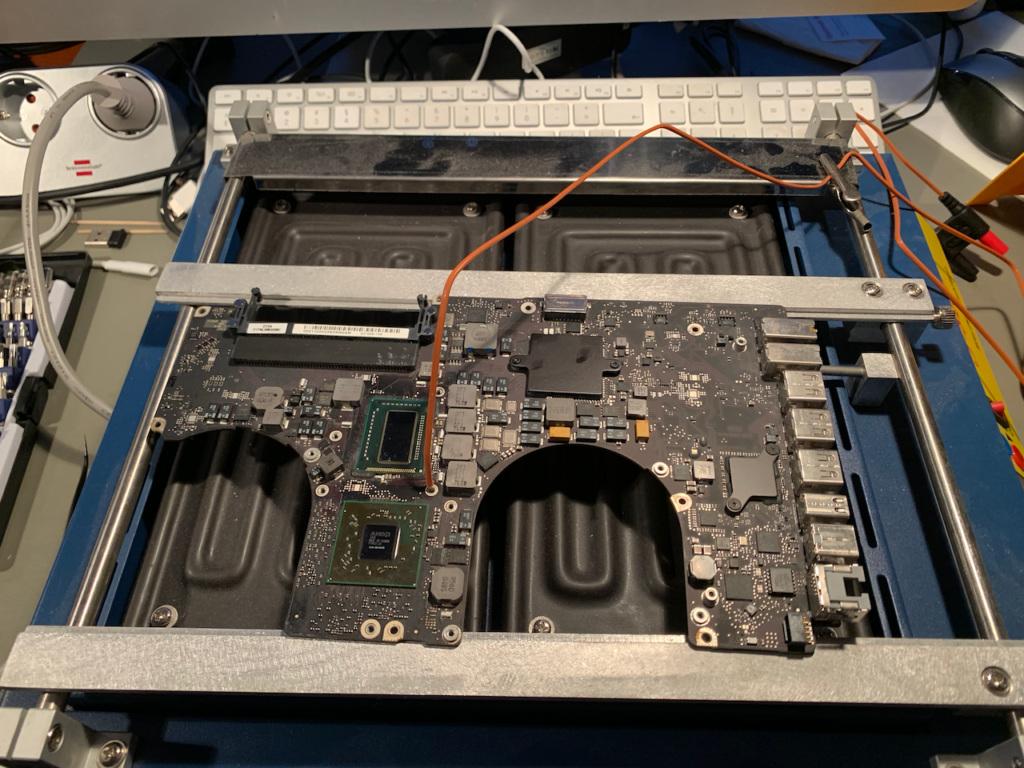
Continue reading “Sad about MacBook Pro”Reflowing a Macbook Pro GPU to no avail
My 2011 Macbook Pro 17″ failed again. A few years back, the GPU went bad so I sent it to a guy in the UK that replaced the GPU, and then it worked for maybe two years. It failed again a couple of months back, but I don’t think it’s worth having it repaired now. I did, however, just do a reflow on it for kicks. It didn’t fix the computer, though, but that won’t stop me from describing what I did. So this is an example of what doesn’t work.
Battery replacement in an iPad Pro
Replacing the battery in an iPad Pro is a horrible, terrible repair procedure. It’s all about heat and glue. Jeez.

ScanSnap generation shift
Almost thirteen years ago, I bought a ScanSnap scanner and hooked it up to the white iMac I had back then. It has worked just fine ever since and has let me scan thousands of documents, eliminating almost all the ring binders that used to dominate my home office.
Continue reading “ScanSnap generation shift”A very disinfected stethoscope
A couple of years ago I bought a Littmann 3200 electronic stethoscope. Love the thing. Fantastic (and adjustable) sound and recording capability and Bluetooth connection to upload those sounds to a companion app.
A couple of weeks back, the stethoscope started to glitch. Every now and then it would hard reset when I pressed the “-” button so I thought that was the end of it. I ordered a new one, planning on disassembling the old one once I had another good one. Today was that day.
Continue reading “A very disinfected stethoscope”Is there life after Crashplan?
Now that Crashplan for home is gone, or at least not long for this world, a lot of people will need to find another way of backing up their stuff. It’s tempting to get angry, and there are reasons to be, but in the end you have to forget about all that and move on. Even though you may have months, or even a year, before Crashplan stops working, there is another reason you have to get something up right now, namely file histories.
iPad Pro: it really is something else
I’ve had the iPad Pro and the Logitech Create keyboard now for a couple of days and it’s really very, very different from what iPads used to be. I’m coming from the first iPad Retina, so it’s been a couple of generations in between.
I’ve never before succeeded in writing anything more that emails with a short “yes” or “no”, or maybe a sentence, from any iPad or iPhone. It simply never was worth the pain. Now, I’m writing this very blog post on the iPad Pro. Using the Logitech keyboard, of course (there are limits; I’m still not prepared to attempt using an on-screen keyboard).
I’m using 1Password for all my logins, and it used to be that any login would be an “oh, no, not again” moment, since it would require switching to 1Password, logging in to it slowly and painstakingly, painfully copying the password, memorising the user name, switching back to the original app, manually entering the user name, painfully (usually takes two or three tries) getting the password “paste” option, then pasting the password, then finally logging in. Now I can slide in the screen from the right, select 1Password there, open it with my thumbprint (YES!), select the username, copy it using cmd-C (!), switch back to Safari (or whatever app I’m in) with cmd-tab, select the password field (if it isn’t still selected) and hit cmd-V. Just like on a desktop or laptop. Most of the keyboard shortcuts we use on a laptop work, like cmd-tab, cmd-X/C/V, cmd-space for search. You’ve got cursor keys on the Logitech keyboard. They’ve also implemented cmd-arrow to go to the beginning and end of lines, and top and bottom of the document. Free at last!
My productivity on the iPad has gone up tenfold, from almost zero to near desktop level. It’s for all practical purposes as productive as a laptop, but with the added ability to be comfortably used for reading, and drawing/annotations with a pen (which I haven’t gotten yet).
I’m missing only a few apps on the iPad, most notably Apple Remote Desktop. I’m not seeing all that much justification, except for this, for keeping a Macbook Air. Especially since the Air’s screen is atrociously bad compared to the iPad Pro’s screen.
So, no, this isn’t just another iPad, this is a game changer.


